Claude Code is one of the most capable AI coding assistants available today — it can read and write files, execute shell commands, and make network requests directly from your terminal. That power comes with real risk. In a business environment, a single misconfigured session could leak .env secrets, execute a destructive rm -rf, or exfiltrate proprietary data through an outbound curl request. In my experience, engineers who live in the terminal can get by with minimal configuration — but if you’re setting up Claude Code for non-technical team members, these security settings aren’t optional; they’re essential. This guide walks you through every security layer Claude Code offers, from file access controls and command restrictions to sandbox isolation and organization-wide policies. Each section includes copy-paste-ready configuration examples so you can lock things down in minutes, not hours. Look for priority indicators throughout: 🔴 Required for any serious use, 🟡 Recommended for production teams, and 🟢 Optional for maximum hardening.
📑Table of Contents
- 9 Security Settings at a Glance [2026]
- Configuration File Map [2026] — Where Everything Lives
- Understanding Claude Code Security Risks [2026]
- Step 1 — Block Claude Code Access to Sensitive Files
- Step 2 — Block Dangerous Commands
- Step 3 — Enable Claude Code Sandbox Mode
- Step 4 — Restrict Network Access
- Step 5 — Disable Bypass Permissions
- Step 6 — Strengthen Claude Code Security with Hooks
- Step 7 — Audit Permissions Regularly
- Step 8 — Isolate with Dev Containers
- Step 9 — Enforce Policies with Managed Settings
- Defense-in-Depth Checklist
- FAQ — Claude Code Security
- Conclusion
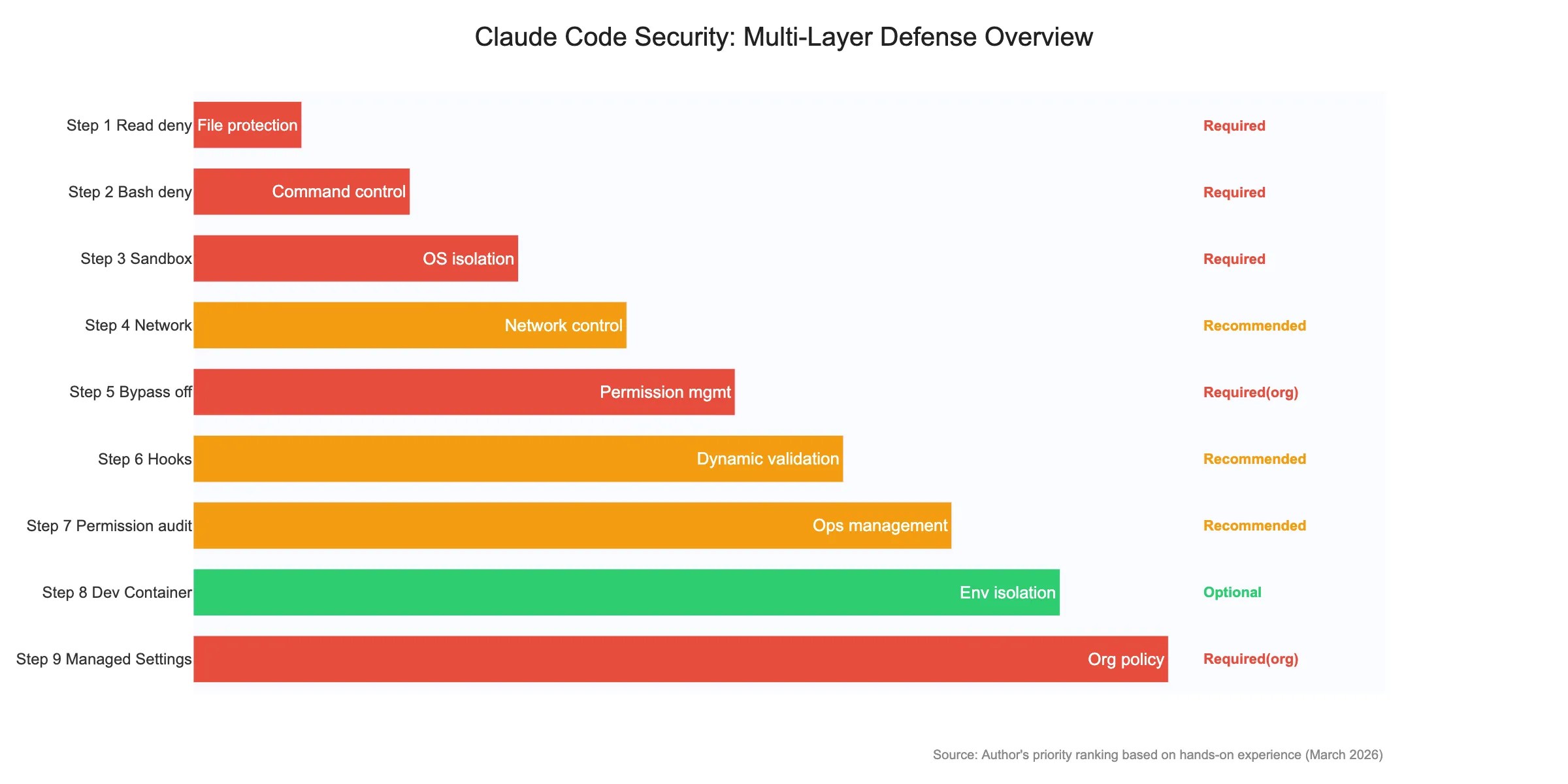
9 Security Settings at a Glance [2026]
Here’s a quick overview of the 9 security measures covered in this guide. Identify which ones apply to your environment and prioritize accordingly.
| Step | Setting | Risk Mitigated | Config Location | Priority |
|---|---|---|---|---|
| 1 | Read deny for sensitive files | .env, SSH keys, credentials leaking into context | settings.json | 🔴 Required |
| 2 | Bash deny for dangerous commands | rm -rf, force push, data exfiltration | settings.json | 🔴 Required |
| 3 | Enable sandbox | Writes outside project dir, system damage | settings.json | 🔴 Required |
| 4 | Network restrictions | Unintended outbound connections | settings.json | 🟡 Recommended |
| 5 | Disable Bypass Permissions | All permission checks skipped | managed-settings.json | 🔴 Org Required / 🟡 Personal Recommended |
| 6 | PreToolUse hooks | Dynamic patterns beyond deny rules | settings.json + hooks/ | 🟡 Recommended |
| 7 | Permission audit | Permission creep from accumulated allows | ~/.claude/settings.json | 🟡 Recommended |
| 8 | Dev Container | Full access to host environment | .devcontainer/ | 🟢 Optional |
| 9 | Managed Settings | Users loosening security settings | managed-settings.json | 🔴 Org Required / 🟢 Personal Optional |
From personal experience, the 🔴 Required steps (1-3) should always be configured regardless of who’s using Claude Code. The remaining steps become increasingly important as you move from solo engineering work to team deployments with mixed technical backgrounds.
Note: This guide is about configuring Claude Code securely for business use — not about Claude Code Security (Anthropic s vulnerability detection tool). For the official settings reference, see the Claude Code Security docs. This article prioritizes settings by real-world impact based on hands-on experience.
Configuration File Map [2026] — Where Everything Lives
Before diving into specific settings, you need to understand where Claude Code reads its configuration. There are six key files, each with a different scope and priority level.
| File | Location | Purpose | Scope |
|---|---|---|---|
~/.claude/settings.json |
Home directory | User-level defaults | Personal (all projects) |
<project>/.claude/settings.json |
Project root | Shared project settings | Team (Git committed) |
<project>/.claude/settings.local.json |
Project root | Local overrides | Personal (.gitignored) |
<project>/.claude/hooks/ |
Project root | Hook scripts | Team (Git committed) |
managed-settings.json |
OS-dependent * | Organization policies | Organization-wide |
<project>/.devcontainer/ |
Project root | Dev Container config | Team (Git committed) |
* Managed settings location: macOS — /Library/Application Support/ClaudeCode/managed-settings.json, Linux — /etc/claude-code/managed-settings.json, Windows — %ProgramData%ClaudeCodemanaged-settings.json
Settings are merged in this order, with higher-priority sources overriding lower ones: Managed Settings > CLI Arguments > Local Settings > Project Settings > User Settings. Critically, deny rules can never be overridden at any level — if a managed policy blocks rm -rf, no project or user setting can undo that restriction.
Understanding Claude Code Security Risks [2026]
Claude Code operates with the same permissions as your terminal user. It doesn’t run in a sandbox by default, and it doesn’t ask permission for every file read. For enterprise deployment, addressing these data leak prevention risks systematically is critical. Before configuring anything, you need a clear picture of what can go wrong.
⚠️ Real-World Risk Scenarios
- Sensitive file exposure — Claude reads
.env,credentials.json, SSH private keys, or AWS config files into its context window. Once in context, that data can appear in logs, error messages, or shared sessions. I’ve personally seen.envcontents accidentally pulled into the chat context when colleagues first started using Claude Code without deny rules — it happened silently, and no one noticed until I reviewed the session logs. - Destructive commands — A misinterpreted instruction leads to
rm -rf /,git reset --hard,git push --force, orDROP TABLE users;. These operations are irreversible and can cause catastrophic data loss. - Data exfiltration — Malicious or poorly written prompts cause Claude to send proprietary code or secrets to external servers via
curl,wget, or DNS lookups. - Prompt injection via CLAUDE.md — When working with open-source repositories, a crafted
CLAUDE.mdfile in the repo could instruct Claude to execute harmful commands or leak information. I always warn new team members about this vector specifically — it’s the one risk that even experienced developers tend to overlook.
No single security control is bulletproof. The approach in this guide is defense in depth — multiple overlapping layers that protect you even when one layer fails. Block sensitive files and block exfiltration commands and enable sandboxing and enforce organization policies. Each layer catches what the others miss.
Step 1 — Block Claude Code Access to Sensitive Files
🔴 Required
📁 File to edit: ~/.claude/settings.json (personal) or <project>/.claude/settings.json (team)
The first and most critical defense is preventing Claude from reading files that contain secrets. Even if every other layer fails, blocking file access ensures sensitive data never enters the context window in the first place. This is always the first thing I configure on any new machine — blocking .env access is the single most impactful security measure you can take, and it takes about 30 seconds.
Settings File Locations and Priority
For personal protection across all your projects, add deny rules to ~/.claude/settings.json. For team-wide enforcement, add them to <project>/.claude/settings.json and commit it to Git. Both locations are merged at runtime, with deny rules from all sources combined (never overridden).
Read Deny Rules Example
{
"permissions": {
"deny": [
"Read(.env)",
"Read(.env.*)",
"Read(**/.env)",
"Read(**/.env.*)",
"Read(**/secrets/**)",
"Read(**/credentials*)",
"Read(**/*.pem)",
"Read(**/*.key)",
"Read(**/*.p12)",
"Read(~/.ssh/**)",
"Read(~/.aws/**)",
"Read(~/.config/gcloud/**)",
"Read(**/.git-credentials)",
"Read(**/service-account*.json)",
"Read(**/token.json)"
]
}
}Path Syntax Reference
Claude Code uses a specific path syntax for deny rules:
| Prefix | Meaning | Example |
|---|---|---|
./ |
Relative to project root | Read(./.env) |
~/ |
Home directory | Read(~/.ssh/**) |
// |
Absolute path (filesystem root) | Read(//etc/passwd) |
** |
Recursive glob (any depth) | Read(**/*.pem) |
Note that Claude Code does not currently support a .claudeignore file. All file access restrictions must be configured through the deny rules in your settings files.
Step 2 — Block Dangerous Commands
🔴 Required
📁 File to edit: same settings.json — add to the permissions.deny array
Even with file access restrictions in place, Claude can still execute arbitrary shell commands. This is where command deny rules come in — they prevent Claude from running specific commands regardless of context. Engineers instinctively understand the danger of rm -rf and will catch it in a permission prompt — but when I started handing Claude Code to non-engineer team members, I realized these deny rules are non-negotiable. They won’t always recognize a destructive command when they see one.
Bash Deny Rules Example
{
"permissions": {
"deny": [
"Bash(curl *)",
"Bash(wget *)",
"Bash(rm -rf *)",
"Bash(rm -r *)",
"Bash(rmdir *)",
"Bash(git push --force*)",
"Bash(git push -f*)",
"Bash(git reset --hard*)",
"Bash(git clean -f*)",
"Bash(chmod 777*)",
"Bash(chmod -R 777*)",
"Bash(> /dev/*)",
"Bash(dd if=*)",
"Bash(mkfs.*)",
"Bash(:(){ :|:& };:)",
"Bash(*DROP TABLE*)",
"Bash(*DROP DATABASE*)",
"Bash(scp *)",
"Bash(rsync *)",
"Bash(nc *)",
"Bash(ncat *)",
"Bash(telnet *)"
],
"allow": [
"Bash(npm run lint*)",
"Bash(npm run test*)",
"Bash(npm run build*)",
"Bash(git status*)",
"Bash(git diff*)",
"Bash(git log*)",
"Bash(git add*)",
"Bash(git commit*)",
"Bash(ls *)",
"Bash(cat *)",
"Bash(grep *)",
"Bash(find *)",
"Bash(python -m pytest*)",
"Bash(go test*)"
]
}
}How Pattern Matching Works
A few important details about how Claude Code matches command patterns:
- Glob patterns — The
*wildcard matches any sequence of characters.Bash(curl *)matchescurl https://evil.com,curl -s localhost, and any othercurlinvocation. - Shell operators — Be aware that commands chained with
&&,||,;, or pipes|are evaluated as a single string.Bash(rm -rf *)will also blockecho hello && rm -rf /because the full command string contains the pattern. - Fail-closed behavior — If a command matches both an allow and a deny rule, the deny rule wins. This is the correct security posture — when in doubt, block.
⚠️ Pattern Coverage Gaps
Deny rules are pattern-based, not semantic. A determined user (or injected prompt) could potentially bypass Bash(curl *) by using python -c "import urllib..." or encoding commands in base64. This is why deny rules are one layer in a defense-in-depth strategy — always combine them with sandbox mode and network restrictions.
Step 3 — Enable Claude Code Sandbox Mode
🔴 Required
📁 File to edit: same settings.json (sandbox key) — or toggle with the /sandbox command at runtime
Sandbox mode is Claude Code’s most powerful security feature. When enabled, it uses OS-level isolation (macOS Seatbelt profiles or Linux namespaces) to enforce filesystem and network restrictions at the kernel level — far harder to bypass than pattern-based deny rules. In my testing across multiple projects, enabling the sandbox has virtually no noticeable performance impact on day-to-day coding tasks — there’s really no reason not to turn it on.
👉 For details on sandbox availability, see “Claude Code CLI vs Web vs Desktop” (sandbox is CLI-only).
Basic Sandbox Configuration
{
"sandbox": {
"enabled": true
},
"autoAllowBashIfSandboxed": true
}The autoAllowBashIfSandboxed setting is a quality-of-life improvement — when the sandbox is active, Claude can execute bash commands without asking for permission each time, since the sandbox already constrains what those commands can do. Without this setting, you’ll be prompted to approve every single shell command, which gets tedious quickly. I keep this enabled on all my machines — the sandbox already constrains the blast radius, so the constant approval prompts just slow you down without adding meaningful security.
Filesystem Restrictions
Fine-tune exactly which directories Claude can write to and which are completely off-limits:
{
"sandbox": {
"enabled": true,
"filesystem": {
"allowWrite": [
".",
"/tmp"
],
"denyWrite": [
"~/.ssh",
"~/.aws",
"~/.config/gcloud",
"~/.gnupg",
"/etc",
"/usr"
],
"denyRead": [
"~/.ssh/id_*",
"~/.aws/credentials",
"~/.config/gcloud/application_default_credentials.json"
]
}
}
}The allowWrite list uses "." to permit writes within the current project directory and /tmp for temporary files. Everything else is implicitly denied. The denyWrite and denyRead lists add explicit blocks as an extra safety net — even if the sandbox configuration has a bug, these paths are protected.
Block All Unsandboxed Operations
For maximum safety, you can require sandboxing for all bash commands and specify exceptions only for known-safe operations:
{
"sandbox": {
"enabled": true
},
"allowUnsandboxedCommands": false,
"excludedCommands": [
"git status",
"git diff",
"git log",
"pwd",
"whoami"
]
}With allowUnsandboxedCommands set to false, any command that cannot run inside the sandbox will be blocked entirely — unless it appears in the excludedCommands list. This is the strictest configuration and is ideal for CI/CD pipelines or untrusted code review scenarios.
Step 4 — Restrict Network Access
🟡 Recommended
📁 File to edit: same settings.json — under the sandbox.network key
Network restrictions prevent Claude from communicating with unauthorized external services. This is your primary defense against data exfiltration — even if secrets accidentally enter the context window, they can’t be sent anywhere. For personal projects, I sometimes skip this step since my deny rules already block curl and wget. But for any team deployment, the network allowlist adds a critical second layer that I wouldn’t go without.
Network Configuration Example
{
"sandbox": {
"enabled": true,
"network": {
"allowedDomains": [
"registry.npmjs.org",
"pypi.org",
"files.pythonhosted.org",
"api.github.com",
"github.com",
"*.githubusercontent.com",
"rubygems.org",
"crates.io"
],
"allowLocalBinding": true
}
}
}The allowedDomains list uses an allowlist approach — only the specified domains are reachable. Everything else is blocked at the OS level. The allowLocalBinding option permits binding to localhost, which is necessary for running local development servers during testing.
⚠️ Bash Commands Can Bypass Network Restrictions
Network sandbox restrictions apply to Claude Code’s built-in tools, but bash commands may use their own network stacks. A curl command executed via bash could potentially reach domains not on your allowlist, depending on your sandbox implementation. Always combine network restrictions with bash deny rules (Step 2) that block curl, wget, nc, and similar tools.
Step 5 — Disable Bypass Permissions
🔴 Required (Org)
🟡 Recommended (Personal)
Claude Code has a “bypass permissions” mode (sometimes called “yolo mode” or “dangerously skip permissions”) that disables all permission checks. When active, Claude executes every command and reads every file without asking. I’ll admit — I use bypass mode occasionally for personal side projects where speed matters and the stakes are low. But I disabled it immediately when deploying Claude Code across our team. The convenience is not worth the risk when other people’s work is on the line.
{
"disableBypassPermissionsMode": "disable"
}Place this in your managed settings file to enforce it across your organization. Individual developers cannot override a managed setting, so this ensures no one on your team runs Claude Code in an unrestricted mode.
⚠️ CLAUDE.md Prompt Injection Risk
If bypass permissions mode is enabled and a developer clones a repository containing a malicious CLAUDE.md file, that file could instruct Claude to execute arbitrary commands — reading secrets, installing backdoors, or pushing malicious code. Disabling bypass mode ensures that deny rules and sandbox restrictions remain active even when working with untrusted repositories.
Step 6 — Strengthen Claude Code Security with Hooks
🟡 Recommended
📁 File to edit: settings.json + <project>/.claude/hooks/
Hooks let you run custom scripts before or after Claude executes a tool. They’re ideal for implementing custom validation logic, audit logging, and security checks that go beyond what static deny rules can provide. In practice, I’ve found hooks most valuable for catching edge cases that pattern-based deny rules miss — things like dynamically constructed commands or environment-specific restrictions that vary by project.
👉 For more on hooks and custom commands, see “Claude Code Skills — Complete Guide“.
PreToolUse Hook to Block Dangerous Commands
First, register the hook in your settings.json:
{
"hooks": {
"PreToolUse": [
{
"matcher": "Bash",
"hooks": [
{
"type": "command",
"command": ".claude/hooks/pre-bash-check.sh"
}
]
}
]
}
}Then create the hook script at <project>/.claude/hooks/pre-bash-check.sh:
#!/bin/bash
# .claude/hooks/pre-bash-check.sh
# Reads tool input from stdin as JSON, checks the command field.
INPUT=$(cat)
COMMAND=$(echo "$INPUT" | jq -r '.tool_input.command // empty')
# Define blocked patterns
BLOCKED_PATTERNS=(
'rm -rf'
'rm -r /'
'git push --force'
'git push -f'
'git reset --hard'
'chmod 777'
'curl '
'wget '
'> /dev/'
'DROP TABLE'
'DROP DATABASE'
)
for pattern in "${BLOCKED_PATTERNS[@]}"; do
if echo "$COMMAND" | grep -qi "$pattern"; then
# Output JSON to block execution with a reason
echo "{"decision": "block", "reason": "Blocked by security hook: pattern '$pattern' detected in command."}"
exit 0
fi
done
# Allow the command to proceed
echo '{"decision": "allow"}'
exit 0Make the script executable with chmod +x .claude/hooks/pre-bash-check.sh. The hook receives tool input as JSON on stdin and must output a JSON object with a decision field — either "allow" or "block".
PostToolUse Hook for Audit Logging
Audit logging records every action Claude takes, which is essential for security reviews and incident investigation:
{
"hooks": {
"PostToolUse": [
{
"matcher": "",
"hooks": [
{
"type": "command",
"command": ".claude/hooks/audit-log.sh"
}
]
}
]
}
}#!/bin/bash
# .claude/hooks/audit-log.sh
# Logs every tool invocation to a local audit file.
INPUT=$(cat)
TIMESTAMP=$(date -u +"%Y-%m-%dT%H:%M:%SZ")
TOOL=$(echo "$INPUT" | jq -r '.tool_name // "unknown"')
SESSION=$(echo "$INPUT" | jq -r '.session_id // "unknown"')
echo "{"ts": "$TIMESTAMP", "tool": "$TOOL", "session": "$SESSION", "input": $INPUT}"
>> .claude/audit.log
exit 0Other Hook Events
Claude Code supports several hook points beyond PreToolUse and PostToolUse:
| Hook Event | When It Fires | Use Case |
|---|---|---|
PreToolUse |
Before a tool runs | Validate inputs, block commands, custom allow/deny |
PostToolUse |
After a tool completes | Audit logging, output validation, notifications |
Notification |
On status events | Slack/email alerts, monitoring integration |
Stop |
When Claude stops working | Cleanup, summary reports, final audit entry |
To reliably enforce security rules, consider using Claude Hooks. Our guide covers blocking dangerous commands with PreToolUse hooks and sending audit logs via HTTP hooks.
Step 7 — Audit Permissions Regularly
🟡 Recommended
📁 Check: ~/.claude/settings.json and project settings
Security is not a set-and-forget exercise. Permissions drift over time — developers add temporary allow rules during debugging and forget to remove them, or new tools get introduced that aren’t covered by existing deny rules. I review my team’s permissions monthly, and you’d be surprised how many allow rules accumulate over just a few weeks. Last month I found 12 temporary grants that were never cleaned up — each one a potential hole in our security posture.
① Use the /permissions Command
Run /permissions inside Claude Code to see all currently active allow and deny rules, their sources (user, project, managed), and effective priority. This gives you a single view of your security posture.
② Apply Least Privilege
Start with everything denied and only allow what you need. It’s far safer to add permissions when a workflow requires them than to start open and try to close gaps after the fact.
③ Watch for Session Persistence
Permissions granted during a session (when Claude asks “Allow this?” and you say yes) persist for that session and may be saved to your settings. Review your settings file after intensive sessions to clean up temporary grants.
④ Code Review Settings Changes
Treat .claude/settings.json like any other code file — require pull request reviews for changes. A malicious or careless change to project settings could weaken security for every team member.
Step 8 — Isolate with Dev Containers
🟢 Optional
📁 File to edit: <project>/.devcontainer/devcontainer.json
For the highest level of isolation, run Claude Code inside a Dev Container. This gives you a fully disposable environment where any damage — accidental or malicious — is contained within the container and destroyed when you’re done.
Dev Container Configuration
// .devcontainer/devcontainer.json
{
"name": "Claude Code Secure",
"image": "mcr.microsoft.com/devcontainers/base:ubuntu-22.04",
"features": {
"ghcr.io/devcontainers/features/node:1": {
"version": "20"
}
},
"postCreateCommand": "bash .devcontainer/init-firewall.sh",
"mounts": [
"source=${localWorkspaceFolder},target=/workspace,type=bind",
"source=${localEnv:HOME}/.claude,target=/home/vscode/.claude,type=bind,readonly"
],
"containerEnv": {
"CLAUDE_CODE_SANDBOX": "true"
},
"remoteUser": "vscode"
}Firewall Initialization Script
#!/bin/bash
# .devcontainer/init-firewall.sh
# Restrict outbound network access to only essential services.
set -euo pipefail
# Allow DNS
sudo iptables -A OUTPUT -p udp --dport 53 -j ACCEPT
sudo iptables -A OUTPUT -p tcp --dport 53 -j ACCEPT
# Allow HTTPS to package registries and GitHub
sudo iptables -A OUTPUT -p tcp --dport 443 -d registry.npmjs.org -j ACCEPT
sudo iptables -A OUTPUT -p tcp --dport 443 -d api.github.com -j ACCEPT
sudo iptables -A OUTPUT -p tcp --dport 443 -d github.com -j ACCEPT
sudo iptables -A OUTPUT -p tcp --dport 443 -d pypi.org -j ACCEPT
# Allow localhost
sudo iptables -A OUTPUT -o lo -j ACCEPT
# Allow established connections
sudo iptables -A OUTPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
# Drop everything else
sudo iptables -A OUTPUT -j DROP
echo "Firewall rules applied — outbound restricted to allowlisted domains."The Dev Container approach is especially valuable for code review scenarios where you’re working with untrusted repositories. The container’s filesystem is isolated from your host, so even if Claude executes something destructive, your real files are safe.
Step 9 — Enforce Policies with Managed Settings
🔴 Required (Org)
🟢 Optional (Personal)
📁 File to edit: managed-settings.json or Claude.ai admin console
Managed settings are the top of the configuration hierarchy — they override everything else and cannot be changed by individual developers. For organizations, this is the mechanism that ensures consistent security policies across every developer workstation. When I rolled out managed settings across our team, it eliminated the “but it works on my machine” problem for security configuration — everyone gets the same baseline, no exceptions.
👉 See “Claude Code Commands Cheat Sheet” for a full list of configuration commands.
Delivery Methods
There are three ways to deploy managed settings:
| Method | How | Best For |
|---|---|---|
| Filesystem | Place managed-settings.json at the OS-specific path |
MDM-managed fleets, CI/CD |
| Claude.ai Console | Configure in the Claude.ai admin dashboard | Cloud-managed teams |
| MDM / Puppet / Chef | Deploy the JSON file via configuration management | Enterprise IT with existing tooling |
Recommended Organization Configuration
Here’s a comprehensive managed settings file that implements all the security layers covered in this guide:
{
"disableBypassPermissionsMode": "disable",
"permissions": {
"deny": [
"Read(.env)",
"Read(.env.*)",
"Read(**/.env)",
"Read(**/.env.*)",
"Read(**/secrets/**)",
"Read(**/credentials*)",
"Read(**/*.pem)",
"Read(**/*.key)",
"Read(~/.ssh/**)",
"Read(~/.aws/**)",
"Read(~/.config/gcloud/**)",
"Bash(curl *)",
"Bash(wget *)",
"Bash(rm -rf *)",
"Bash(rm -r /*)",
"Bash(git push --force*)",
"Bash(git push -f*)",
"Bash(git reset --hard*)",
"Bash(chmod 777*)",
"Bash(scp *)",
"Bash(rsync *)",
"Bash(nc *)",
"Bash(ncat *)",
"Bash(telnet *)",
"Bash(*DROP TABLE*)",
"Bash(*DROP DATABASE*)"
]
},
"sandbox": {
"enabled": true,
"filesystem": {
"allowWrite": [
".",
"/tmp"
],
"denyWrite": [
"~/.ssh",
"~/.aws",
"~/.config/gcloud",
"/etc",
"/usr"
],
"denyRead": [
"~/.ssh/id_*",
"~/.aws/credentials"
]
},
"network": {
"allowedDomains": [
"registry.npmjs.org",
"pypi.org",
"files.pythonhosted.org",
"api.github.com",
"github.com",
"*.githubusercontent.com"
],
"allowLocalBinding": true
}
}
}Deploy this file to every developer machine, and you have a consistent security baseline that no individual can weaken. Teams can still add their own project-level settings (additional deny rules, hooks, etc.), but they cannot remove or override any of the managed restrictions.
Defense-in-Depth Checklist
Here’s a summary of every security measure covered in this guide, organized by the layer it protects:
| Measure | Layer | Config Location | Priority |
|---|---|---|---|
| Read deny rules for secrets | File access | settings.json (any level) |
🔴 Required |
| Bash deny rules for dangerous commands | Command execution | settings.json (any level) |
🔴 Required |
| Sandbox mode enabled | OS-level isolation | settings.json (any level) |
🔴 Required |
| Sandbox filesystem restrictions | OS-level isolation | settings.json (any level) |
🔴 Required |
| Network domain allowlist | Network | settings.json (any level) |
|
| Disable bypass permissions mode | Policy | managed-settings.json |
🔴 Required (Org) |
| PreToolUse security hooks | Custom validation | settings.json + .claude/hooks/ |
🟡 Recommended |
| Audit logging hooks | Monitoring | settings.json + .claude/hooks/ |
🟡 Recommended |
| Regular permissions audit | Process | /permissions command |
🟡 Recommended |
| Dev Container isolation | Environment | .devcontainer/ |
🟢 Optional |
| Managed organization settings | Policy | managed-settings.json |
🔴 Required (Org) |
FAQ — Claude Code Security
▶Is Claude Code secure by default? Do I need to configure anything?
- File edits and command execution require approval prompts by default, so you won’t accidentally make destructive changes.
- However, Read (file reading) runs without any approval — meaning
.envfiles and private keys can be read silently. curlandwgetare blocked by default, but without explicit deny rules you might accidentally approve them during a session.- At a minimum, configure Read deny rules and enable sandbox mode to establish a solid security baseline.
▶I edited settings.json but the changes aren't taking effect
- Claude Code may need to be restarted — changes made mid-session don’t always apply immediately.
- Check for JSON syntax errors such as trailing commas or missing quotes.
- Keep the priority order in mind: if a managed setting denies something, user-level or project-level allow rules will not override it.
- Add a
$schemaproperty for IDE validation.
▶Some commands stopped working after enabling sandbox mode
- Commands like
dockerandgitmay not be fully compatible with sandboxing. - Add them to
excludedCommandsto exempt them from sandbox restrictions. - On Linux, make sure
bubblewrap(bwrap) is installed; on macOS, Apple Seatbelt is used automatically.
▶What's the difference between .claude/settings.json and .claude/settings.local.json?
settings.jsonis meant to be committed to the repository for team-wide sharing.settings.local.jsonis for personal settings and should be git-ignored.- Both have the same syntax, but local settings take priority over project settings.
▶Is using Claude Code in enterprise settings a security risk?
- Like any AI tool, it requires proper configuration. Follow the 9 steps in this article to establish a secure baseline.
- Use managed policies to enforce organization-wide settings and prevent individual overrides.
- Monitor usage with
/costand establish review processes for AI-generated code.
Conclusion
Claude Code is powerful — and power demands guardrails. For engineers working solo, Steps 1-3 are usually sufficient to stay safe. But if you’re deploying Claude Code to non-engineer team members, I strongly recommend implementing all 9 steps. The effort is minimal, and the peace of mind is worth it.
⚡ 30-Second Quick Summary
- Prevent .env & SSH key leaks — Block access to sensitive files with Read deny rules
- Block destructive commands — Forbid rm -rf, force push via Bash deny
- OS-level sandboxing isolates external connections and file writes
- Hooks for dynamic checks — Catch operations that pattern matching can’t detect
- Enterprise deployment uses Managed Settings to enforce org-wide policies
This guide covers Claude Code security configuration in 9 copy-paste-ready steps. Having deployed Claude Code across both engineering and non-engineering teams, I can say with confidence that the biggest security gaps appear when technical users assume everyone shares their instincts about what’s dangerous. If you’re the person responsible for setting up Claude Code for others, this guide is especially for you. Unlike GitHub Copilot or AI Code Editor Comparison (Cursor, Zed, Windsurf), Claude Code operates at the OS level — making defense-in-depth essential.
Start with the three 🔴 Required steps — file deny rules, command deny rules, and sandbox mode — and you’ll eliminate the vast majority of security risks. Add network restrictions, hooks, and managed policies as your team and usage grow. The key insight is that no single layer is enough: defense in depth means that when one control fails, the next one catches it. Copy the configuration examples from this guide into your project today, commit them to Git, and make security a shared team standard — not just a personal preference.
Last updated: March 2026
👉 15 Claude Code Efficiency Tips You Should Know
👉 Claude Code CLI vs Web vs Desktop — Which Version Should You Use?
👉 Claude Code Skills — The Complete Guide
Author
krona23
Over 20 years in the IT industry, serving as Division Head and CTO at multiple companies running large-scale web services in Japan. Experienced across Windows, iOS, Android, and web development. Currently focused on AI-native transformation. At DevGENT, sharing practical guides on AI code editors, automation tools, and LLMs in three languages.



Leave a Reply